
The AI Shadow IT Crisis Is Forcing Enterprises to Rethink Productivity Tools
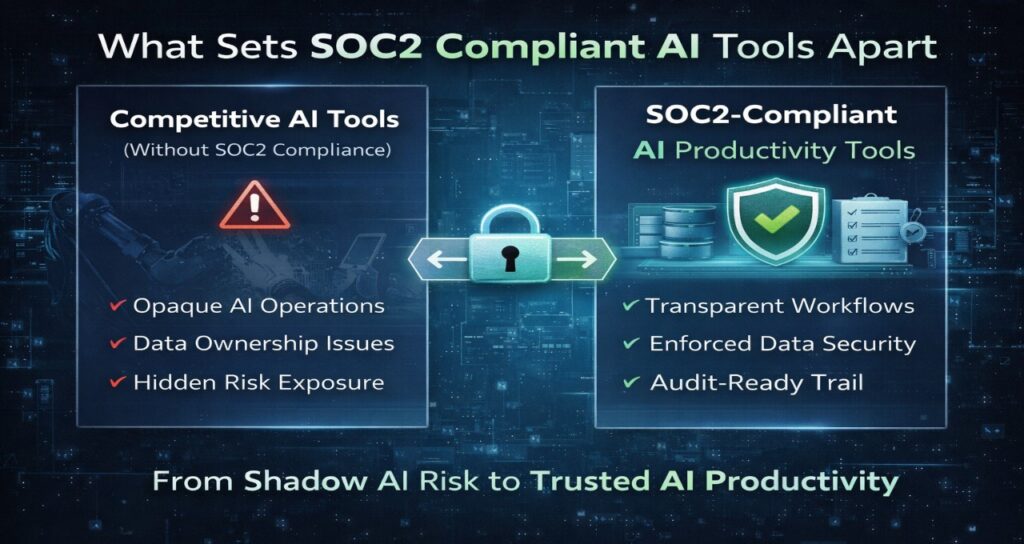
SOC2 compliant AI productivity tools are no longer optional in 2026—they are the foundation of enterprise AI adoption. As organizations move from experimentation to deployment, tools must prove zero data retention, secure model isolation, and continuous audit readiness to be trusted in real-world workflows.
In 2024, companies rushed to adopt AI tools.
In 2026, they’re rushing to control them.
What started as productivity gains quickly turned into an AI Shadow IT crisis—employees using unauthorized tools, feeding sensitive company data into external models, and creating invisible compliance risks.
Now, enterprise buyers are asking a different question:
“Which AI tools are actually safe to deploy?”
That’s where SOC2 compliant AI productivity tools enter the picture. These platforms don’t just enhance productivity—they provide verifiable trust infrastructure that aligns with modern compliance, governance, and audit requirements.
The Trust Stack Framework (Core Technology)
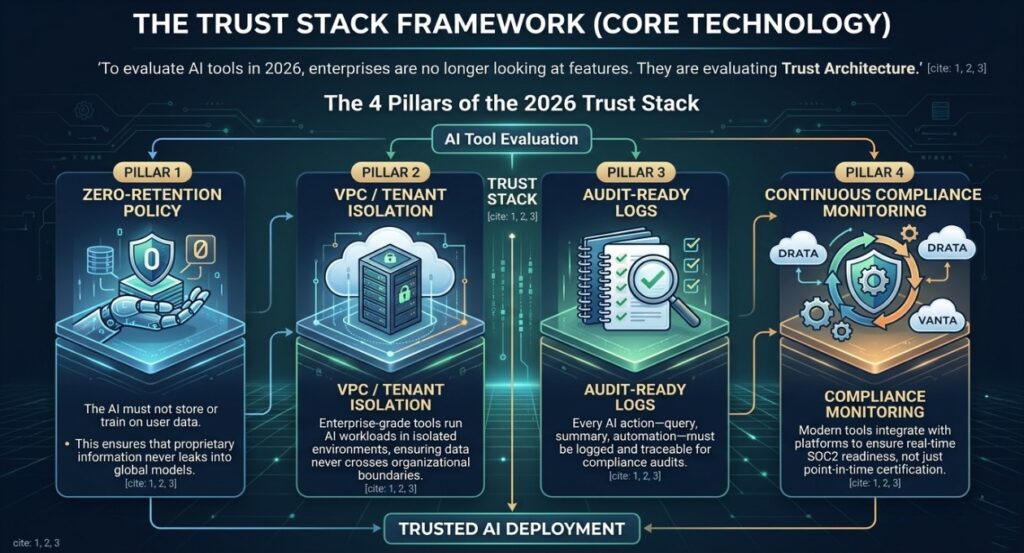
To evaluate AI tools in 2026, enterprises are no longer looking at features.
They are evaluating Trust Architecture.
The 4 Pillars of the 2026 Trust Stack
1. Zero-Retention Policy
The AI must not store or train on user data.
This ensures that proprietary information never leaks into global models.
2. VPC / Tenant Isolation
Enterprise-grade tools run AI workloads in isolated environments, ensuring data never crosses organizational boundaries.
3. Audit-Ready Logs
Every AI action—query, summary, automation—must be logged and traceable for compliance audits.
4. Continuous Compliance Monitoring
Modern tools integrate with platforms like Drata or Vanta to ensure real-time SOC2 readiness, not just point-in-time certification.
Why SOC2 AI Tools Matter Now
The shift toward SOC2 compliance is driven by two major forces.
The Rise of AI Agents in Workflows
AI is no longer just assisting—it’s executing.
Organizations already deploying systems like those explained in AI agents in project management are discovering that automation introduces new risks.
When AI can:
- approve tasks
- generate code
- access internal documents
…it must also be fully auditable and compliant.
The Collapse of “Basic AI Productivity”
Earlier tools focused on speed. Today, enterprises need control.
Many teams initially adopted solutions similar to those highlighted in AI productivity tools for remote teams, but are now replacing them with SOC2-compliant alternatives that meet security standards.
The Governance Layer Is Becoming Mandatory
AI governance is no longer theoretical.
Organizations must now align with frameworks similar to those discussed in conversational AI governance systems, where compliance is embedded directly into AI workflows.
Architecture: How SOC2 AI Systems Work
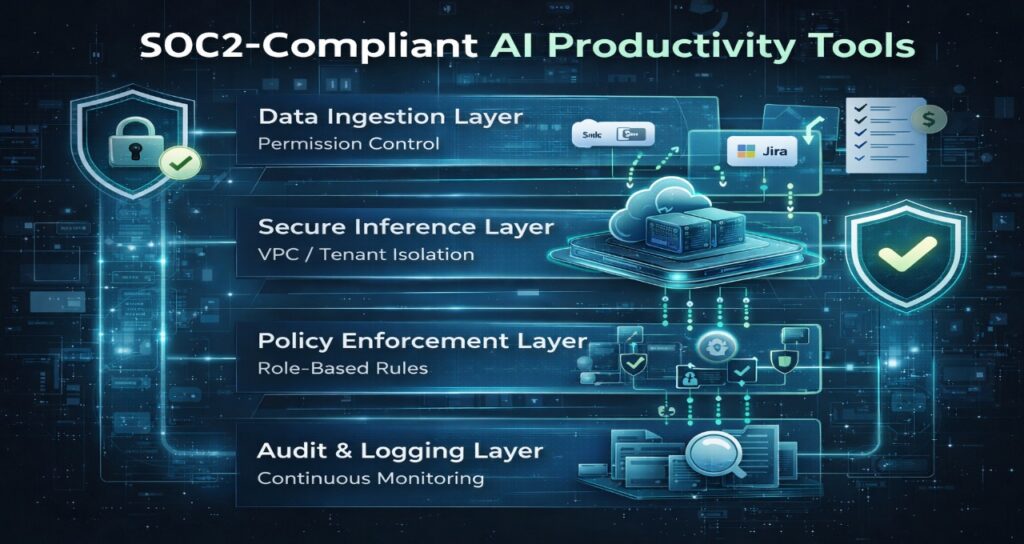
SOC2-compliant AI tools operate on a fundamentally different architecture compared to consumer AI tools.
Data Ingestion Layer
- Connects to internal systems (Slack, Drive, Jira)
- Applies permission controls at ingestion
Secure Inference Layer
- Runs AI models in isolated environments
- Prevents cross-tenant data exposure
Policy Enforcement Layer
- Applies rules such as:
- no external data sharing
- role-based access
- compliance checks
Audit & Logging Layer
- Tracks every AI interaction
- Stores logs for audit review
This architecture ensures that AI productivity does not compromise enterprise security.
Comparison Table — SOC2 AI Productivity Tools (2026)
| Feature | Glean | Read AI | Notion AI |
| SOC2 Status | Type II (Continuous) | Type II (Continuous) | Type II (Continuous) |
| Data Retention | Zero-Training | Zero-Training | No-Training (Enterprise) |
| Isolation Model | Tenant-Siloed VPC | Regional Encryption | Workspace Isolation |
| Audit Logs | Query-Level Logs | Meeting Logs | AI Activity Logs |
| Data Residency | Global Control | EU / US / APAC | US (EU expanding) |
| Key Innovation | Permissions Mirroring | PII Redaction | Private Team Spaces |
Deep-Dive: Leading SOC2 AI Tools
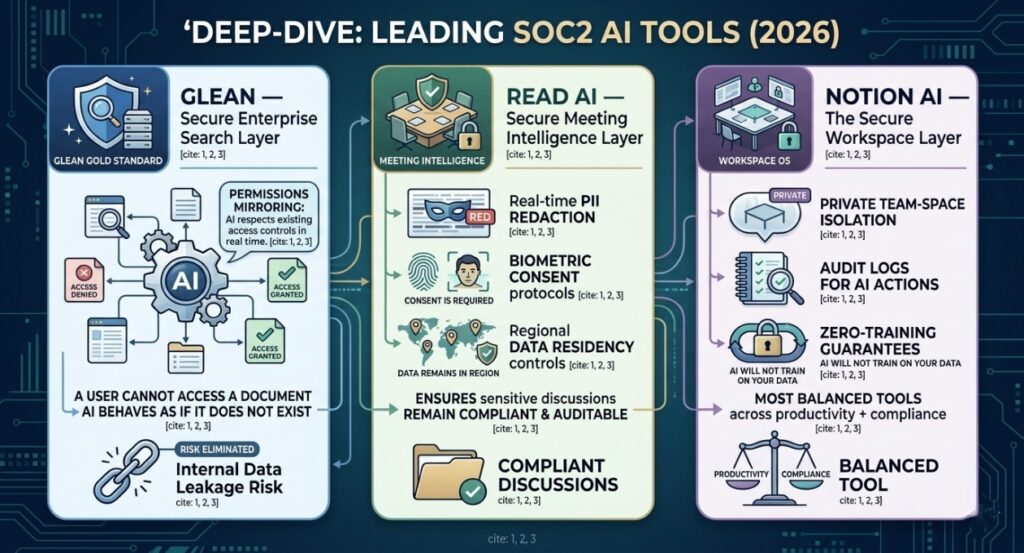
Glean — Secure Enterprise Search Layer
Glean has emerged as the gold standard for SOC2-compliant AI search.
Its core advantage is permissions mirroring, where the AI respects existing access controls in real time. If a user cannot access a document, the AI behaves as if the document does not exist.
This eliminates one of the biggest risks in enterprise AI: internal data leakage.
Read AI — Secure Meeting Intelligence
Meeting intelligence is one of the highest-risk AI categories.
Read AI addresses this with:
- real-time PII redaction
- biometric consent protocols
- regional data residency controls
It ensures that even sensitive discussions remain compliant and auditable.
Notion AI — The Secure Workspace Layer
Notion AI has evolved into a central operating system for enterprise workflows.
Its 2026 upgrades include:
- private team-space isolation
- audit logs for AI actions
- zero-training guarantees
This makes it one of the most balanced tools across productivity + compliance.
The Auditor’s View: Why SOC2 Type II Matters

SOC2 Type I is no longer sufficient for AI systems.
It only proves that controls exist at a single point in time.
SOC2 Type II proves:
- controls are maintained over months
- systems operate securely under real conditions
- compliance is continuous
This matters because AI systems are dynamic.
Models evolve. Prompts change. Data flows constantly.
Without continuous monitoring, compliance quickly becomes outdated.
Strategic Industry Implications
The rise of SOC2 AI tools is reshaping the enterprise software market.
Microsoft
Embedding enterprise-grade AI compliance into productivity tools through secure Copilot environments.
OpenAI
Providing enterprise APIs that ensure no training on customer data, enabling SOC2-aligned deployments.
Nvidia
Powering secure AI infrastructure with GPUs optimized for private inference environments.
Future Outlook (2026–2028)
AI Compliance as Infrastructure
SOC2 is evolving into a standardized trust layer across AI systems.
Programmable Governance
Compliance rules will become programmable, allowing organizations to enforce policies automatically across tools.
Death of Shadow AI
As compliant tools mature, unauthorized AI usage will decline—replaced by enterprise-approved AI ecosystems.
FAQ — SOC2 Compliant AI Productivity Tools
1.What are SOC2 compliant AI productivity tools?
Ans-They are AI tools that meet SOC2 security standards, ensuring data protection, auditability, and controlled access. These tools are designed for enterprise environments where compliance is mandatory.
2.What is the difference between SOC2 Type I and Type II?
Ans-SOC2 Type I evaluates controls at a single point in time. Type II verifies that those controls operate effectively over time, making it essential for AI systems.
3.Do SOC2 AI tools use my data for training?
Ans-No. Enterprise-grade tools provide zero-retention or no-training guarantees, ensuring your data is never used to train AI models.
4.Are async AI tools also SOC2 compliant?
Ans-Some are. Many modern systems, including those discussed in async AI tools for global teams, are evolving to include compliance layers.
5.How do companies ensure AI compliance in 2026?
Ans-Organizations combine SOC2-compliant tools with governance frameworks similar to those outlined in AI watermarking tools for EU compliance, ensuring both technical and regulatory alignment.
Final Thoughts: The 2026 Mandate for AI Sovereignty
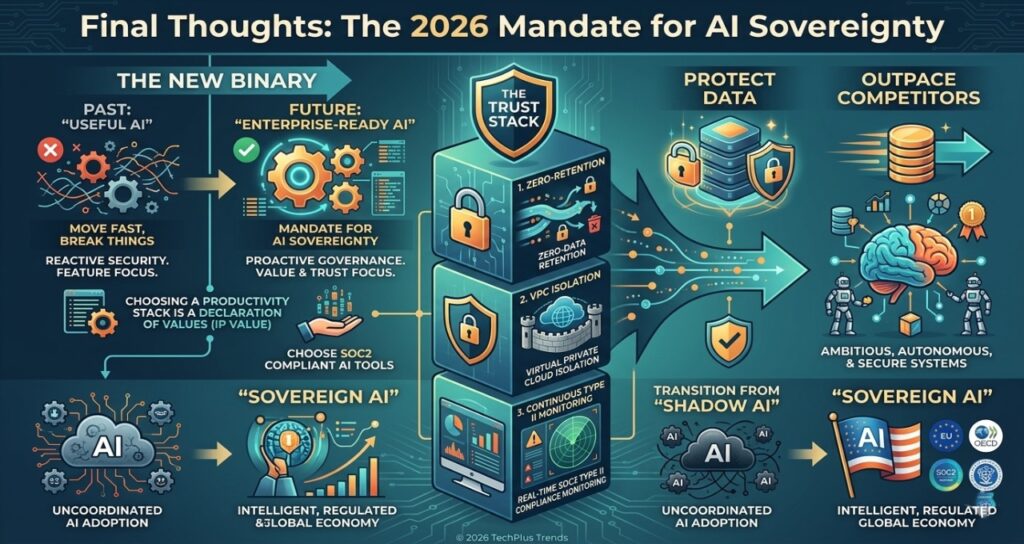
As we move deeper into the age of Agentic Workflows, the distinction between “useful AI” and “enterprise-ready AI” has become binary. The era of the “move fast and break things” approach to AI adoption is officially over, replaced by a mandate for AI Sovereignty.
For founders and technology leaders, the choice of a productivity stack is no longer just a question of features or speed; it is a declaration of how they value their organization’s intellectual property. Choosing SOC2 compliant AI productivity tools is the first step in moving from a reactive security posture to a proactive governance strategy.
In 2026, trust is the ultimate currency. Organizations that build their AI foundations on the Trust Stack—Zero-Retention, VPC Isolation, and Continuous Type II Monitoring—will not only protect their data but will also outpace their competitors by deploying more ambitious, autonomous, and secure systems with total confidence.
The transition from “Shadow AI” to “Sovereign AI” is not just a technical upgrade; it is the necessary evolution for any digital organization scaling in an intelligent, regulated global economy.
Sources
American Institute of CPAs (AICPA) – SOC 2® Reporting Standards and Trust Services Criteria. https://www.aicpa.org/
European Commission – Artificial Intelligence Act (EU AI Act) Transparency & Governance. https://digital-strategy.ec.europa.eu/en/policies/european-ai-act
Gartner – Top Strategic Technology Trends for 2026: AI Trust, Risk and Security Management (TRiSM). https://www.gartner.com/
Nvidia – Secure AI Infrastructure for the Enterprise. https://www.nvidia.com/en-us/ai/
Microsoft – Microsoft 365 Copilot Privacy, Security, and Compliance Documentation. https://www.microsoft.com/en-us/ai
OECD – AI Policy Observatory: Frameworks for Trustworthy AI. https://oecd.ai/
AI Transparency & Editorial Disclosure
Editorial Process & Integrity This technical guide was developed by Tech Plus Trends through a collaborative “Human-in-the-Loop” (HITL) AI workflow. While advanced agentic systems were utilized to synthesize multi-platform compliance data, 2026 security benchmarks, and SOC2 Type II infrastructure trends, the final strategic analysis, “Trust Stack” framework, and editorial conclusions were verified and finalized by Saameer, our founder and lead analyst. We prioritize technical precision over automated volume.
EU AI Act Compliance (Article 50) In accordance with transparency requirements for AI-assisted content, be advised that the analysis of “Agentic Workflows” and “Governance Layers” described herein involve interaction with autonomous AI systems. This content is intended to provide an objective, expert-led analysis of how these technologies function within regulated enterprise environments.
Security & Privacy Disclaimer The information provided in this guide is for educational and analytical purposes only. While we highlight SOC2 Type II compliant tools, the final responsibility for security audits and tool implementation rests with the adopting organization. Tech Plus Trends is not a compliance auditing firm; we recommend consulting with certified SOC2 auditors and legal counsel before deploying AI tools in highly regulated environments.
Author Bio
Saameer is the founder of Tech Plus Trends and an independent technology analyst specializing in AI infrastructure, enterprise software systems, and digital governance. His work focuses on how organizations deploy secure AI workflows, SOC2-compliant systems, and agentic automation to scale productivity without compromising data integrity and compliance.

