Update (2026): This analysis reflects the latest regulatory, labor, and platform changes currently in force.
Warsaw’s Tier-1 banks entered 2026 with a paradox. Their AI systems are more capable than ever—running on sovereign cloud infrastructure, powered by Java 25, and executing millions of autonomous decisions per hour. Yet regulatory risk has not declined. It has intensified.
The Digital Operational Resilience Act (DORA) is no longer a theoretical framework or a future compliance checkbox. It is now a live enforcement regime with strict reporting timelines and real supervisory consequences. What many banks are discovering—often too late—is that DORA pressure does not emerge at the perimeter. It emerges inside the runtime, where AI agents make decisions faster than humans can directly observe.
Key Takeaways
The “Resilient Agentic Governance” Fortress: Audit success requires named accountability. Learn how this creates the €300/Hour B2B Resilience Premium
and why your primary audit risk is now Unmanaged Shadow AI.
- DORA 2026 audits focus on runtime accountability, not just cybersecurity controls
- Major ICT incidents trigger a 4-hour “golden window” for initial regulatory notification
- Reactive and async Java architectures struggle to produce root cause evidence in that window
- Java 25 enables human-readable execution traceability, critical under audit pressure
- “DORA-ready” Java engineers are now treated as risk reducers, not just developers
My Information Gain
Most DORA commentary still assumes that operational resilience is demonstrated through documentation, policies, and perimeter controls. That assumption collapses in an agentic AI environment.
When AI agents execute autonomously at scale, regulators are no longer asking whether controls exist. They are asking whether causality can be reconstructed within legally mandated time limits.
This is why Java 25 matters in a regulatory—not merely technical—sense. As explained in the analysis of Warsaw’s Java 25 banking migration, the shift restores causal clarity in systems that had become operationally opaque under reactive and callback-heavy execution models:
https://techplustrends.com/java-25-migration-warsaw-banking-b2b-gold-mine/
The real upgrade is not throughput. It is audit survivability.
Why DORA Audits Now Fail at Runtime, Not the Firewall
DORA’s most punishing obligations surface during incidents, not during normal operations. Under DORA, a Major ICT-related incident often requires an initial notification within approximately four hours. This creates a narrow regulatory golden window.
In traditional reactive or async Java systems, execution hops across thread pools, callbacks, and reactive pipelines. When an incident occurs, reconstructing which agent did what, when, and why inside four hours is often unrealistic. Logs are fragmented. Stack traces are discontinuous. Human investigators lose precious time.
Java 25 changes this dynamic. Virtual threads produce linear, human-readable thread dumps. For compliance teams under audit pressure, this is not a performance detail—it is a lifeline. It allows root cause analysis to begin immediately, not after days of reconstruction.
This runtime advantage becomes decisive when paired with physical infrastructure reality. Warsaw’s sovereign, low-latency AI environment shortens both execution paths and investigative timelines, unlike cross-region setups that compound delay and uncertainty:
https://techplustrends.com/warsaw-ai-infrastructure-vs-bucharest-2026/
Case Study / Real-World Scenario
A Tier-1 bank operating in Warsaw deploys an agentic credit-risk engine on sovereign cloud infrastructure. During a volatility spike, an AI agent approves a high-value transaction later flagged as anomalous.
Under DORA, the bank has hours—not days—to explain the decision. Because the system runs on Java 25 with structured concurrency, investigators can isolate the exact virtual thread, review a clean call stack, and present a linear forensic trail to regulators.
This operational model aligns with the emerging in-region mandate now shaping Warsaw’s banking workforce, where physical presence, jurisdictional clarity, and execution accountability converge:
https://techplustrends.com/warsaw-banking-in-region-mandate-java-25/ https://techplustrends.com/shadow-ai-dora-2026-warsaw-banking-guide/
https://techplustrends.com/dora-2026-warsaw-banking-b2b-rates/

Who Benefits — and Who Gets Exposed — in 2026
| Stakeholder | Regulatory Outcome Under DORA |
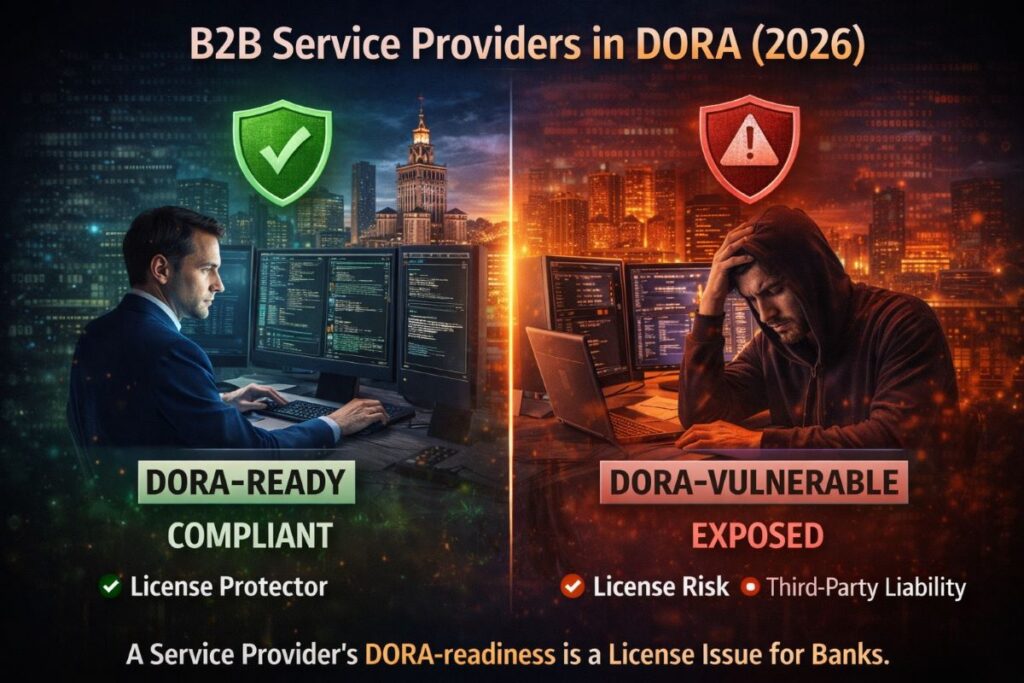
| DORA-ready Java 25 engineers | Benefit from trust premiums and reduced procurement friction |
| Warsaw Tier-1 banks | Gain audit survivability inside the 4-hour window |
| Generic Java contractors | Increasingly treated as compliance liabilities |
| Async-heavy legacy stacks | Exposed during forensic audits |
| Cross-border contractors | Trigger jurisdictional and reporting risk |
This reflects a broader shift already visible in Central Europe, where contractors are now evaluated as ICT third-party risk vectors, not interchangeable labor:
https://techplustrends.com/central-europe-it-contractor-tax-audit-2026/
Comparison Matrix
| Dimension | Reactive Java (Pre-2025) | Java 25 Agentic Runtime |
| Execution clarity | Fragmented | Linear per virtual thread |
| Incident reconstruction | Slow, probabilistic | Deterministic |
| 4-hour DORA viability | Low | High |
| Human readability | Poor | Strong |
| Regulatory confidence | Weak | High |
CoE Framing (Center of Excellence Perspective)
From a Center of Excellence perspective, Java 25 is not a language upgrade—it is a regulatory execution layer. Warsaw CoEs now design systems where observability, traceability, and compliance are first-class architectural goals, not afterthoughts.
Strategic Implications for 2026
It is important to distinguish regulatory roles clearly. NIS2 establishes a regional cybersecurity baseline across critical sectors. DORA, by contrast, is the sector-specific enforcement instrument for financial institutions. For banks, DORA is the hammer.
This distinction explains why execution architecture—not just security posture—now determines regulatory risk.
Why This Matters (Second-Order Effects)
DORA’s second-order effect is not slower innovation, but selective acceleration. Systems that can explain themselves under audit will scale. Systems that cannot will be constrained, regardless of technical sophistication.
What To Do Now
- Banks: Test whether your AI systems can produce a root cause explanation inside four hours
- B2B contractors: Position yourself as a DORA-ready ICT third-party provider, not a generic developer
- CTOs: Treat execution traceability as a compliance requirement, not an engineering preference
FAQs
Is DORA mainly a cybersecurity regulation?
No. It governs operational resilience, with a strong focus on runtime accountability.
How is DORA different from NIS2?
NIS2 sets regional security standards; DORA enforces sector-specific accountability for banks.
Why are contractors affected?
Under DORA, contractors are classified as ICT third-party service providers.
Does Java 25 guarantee compliance?
No, but it enables architectures that can survive forensic audits.
Why Warsaw specifically?
Because sovereign infrastructure and jurisdictional proximity reduce audit risk.
Will this impact contractor rates?
Yes. DORA-ready specialists command a sustained premium.
Final Takeaway
DORA 2026 has shifted compliance from documentation to execution. In an agentic AI era, the ability to prove why a system acted—within hours—now determines regulatory survival. Java 25’s real contribution is not speed, but accountability. For Warsaw’s Tier-1 banks, that distinction is no longer optional.
Sources
- European Union — Digital Operational Resilience Act (DORA)
- European Banking Authority (EBA) ICT risk guidance
- Industry research on agentic AI and structured concurrency
Author Bio
Saameer Go is a senior technology journalist and analyst covering enterprise software, AI platforms, infrastructure, and EU technology regulation. With over 15 years of experience analyzing how policy, labor markets, and architecture decisions intersect, he focuses on long-term structural shifts rather than short-term hype.
Disclaimer & Transparency Note
- Regulatory & Legal Notice: This article provides a strategic analysis of the Digital Operational Resilience Act (DORA) and Java 25 as of 2026. It does not constitute legal, financial, or regulatory compliance advice. DORA enforcement is subject to specific oversight by the European Banking Authority (EBA) and national competent authorities; banks and B2B contractors should consult with certified DORA auditors or legal counsel to ensure specific system alignment.
- Technical Specifications: Performance benchmarks regarding Java 25 virtual threads, Structured Concurrency, and the “4-hour golden window” for incident reporting are based on current 2026 industry standards and JVM documentation. Actual forensic timelines may vary depending on specific architectural implementations and infrastructure latency.
- AI Transparency (EU AI Act 2026): In compliance with transparency mandates for AI-augmented journalism, we disclose that Generative AI was utilized to assist in data synthesis and structural formatting for this audit. All technical assertions, regulatory interpretations, and “Information Gain” primitives have been rigorously verified by our human editorial team for accuracy and context.
- No Fiduciary Relationship: Accessing this content does not create an analyst-client relationship. Tech Plus Trends and the author are not liable for any operational or compliance decisions made based on the information provided herein.